Detection and response
Spot hostile sessions and react before trust is lost.
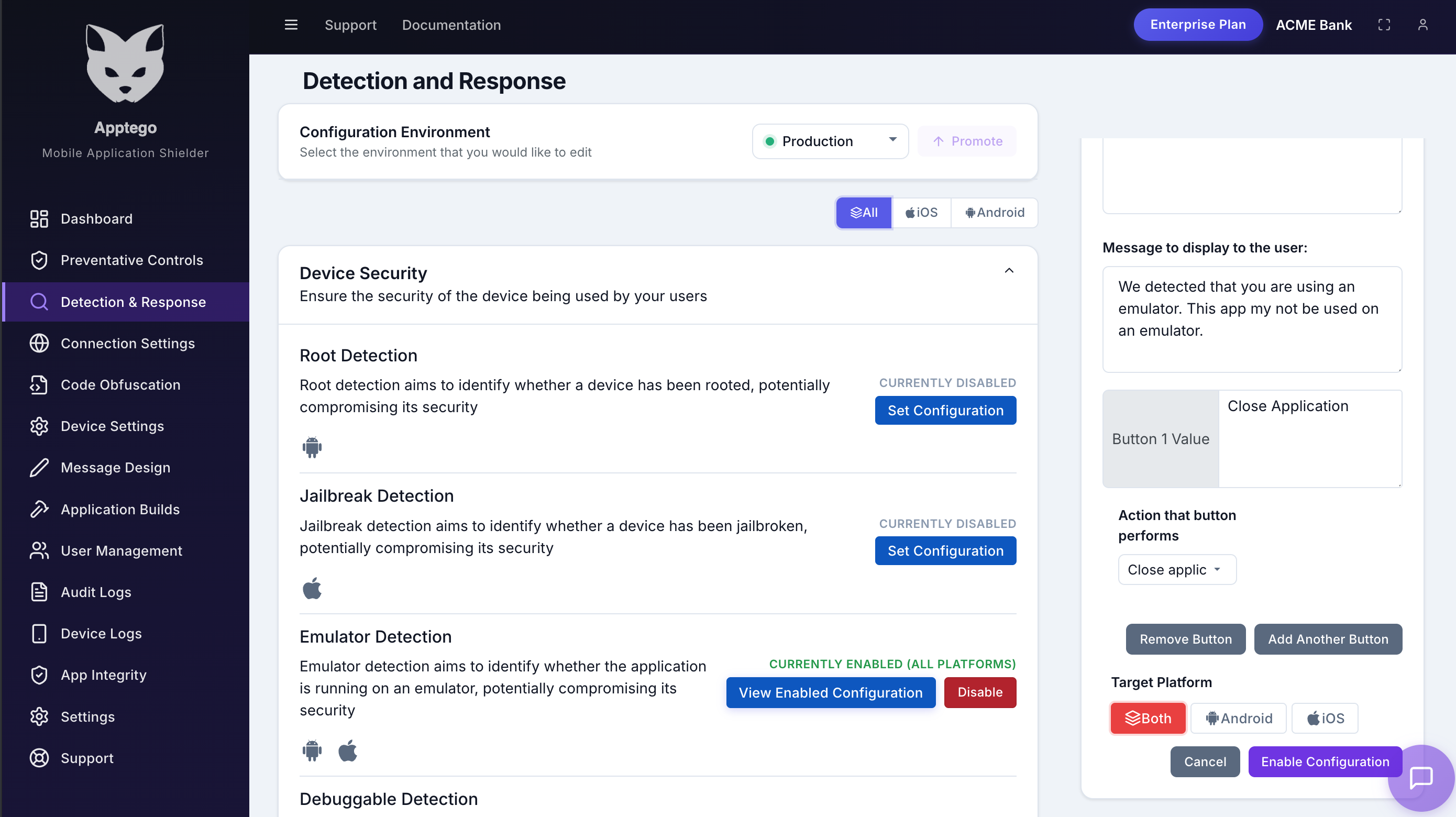
AppTego adds runtime sensors for compromised devices, instrumentation frameworks, tampering, risky network conditions, and policy violations. Each detection can log silently, show a branded message, redirect the user, or terminate the session.
Threat coverage
Built for the runtime conditions attackers rely on.
Detection and response controls are designed for the practical ways mobile apps are attacked after release: rooted and jailbroken devices, dynamic instrumentation, app cloning, virtual containers, tampered binaries, proxy interception, debugger attachment, and screen capture workflows.
- Root and jailbreak detection
- Hook, Frida, and debugger detection
- Emulator and virtual app detection
- Screen capture and recording detection
- Proxy, VPN, and location spoofing detection
- App tamper and integrity checks
Choose the right response for each signal
Not every detection deserves the same action. AppTego lets teams match response severity to user impact, fraud risk, and compliance obligations.
Log silently
Collect event telemetry for investigation, fraud modelling, or phased rollout without interrupting the user.
Warn or guide
Show branded guidance that explains why access is restricted and how the user can recover.
Redirect or close
Move the user to support, policy, or remediation content, or terminate high-risk sessions immediately.